Executive Brief
Your daily threat summary — overall risk score, key metrics, and actionable alerts.
Risk score updated daily
Free · Ungated · Updated nightly
3,623 incidents. 4.2B individuals affected. 7 federal, regulatory, and community sources unified into twelve analytical views. No login. No subscription.
No account required · Opens immediately
3,623
Threat incidents indexed
Updated nightly
4.2B
Individuals affected
All-time total
7
Data sources unified
Federal + community
12
Analytical views
Exec → predictive
Intelligence views
From executive summary to predictive modeling to attack chain visualization — every view is built for independent practices that need to understand their threat environment, not just receive a compliance score.
Your daily threat summary — overall risk score, key metrics, and actionable alerts.
Risk score updated daily
All incidents across all sources, timeline, breakdown by vector, source, and entity type.
188% increase vs prior period
Risk-ranked directory of every healthcare entity with incident histories and relationship networks.
Top entity risk score: 98/100
Searchable, sortable table of every threat record. Export to CSV for compliance documentation.
Full dataset · exportable
Choropleth heat map with incident markers across all 50 states — all 7 sources visible simultaneously.
All US states covered
Statistical projection of future incident volume with 95% confidence band and anomaly detection.
0.3 incidents/month trend rate
Sankey diagram: source → vector → entity type → severity outcome.
71 unique vectors mapped
Compliance performance metrics tied to real breach outcomes.
OCR resolution agreements, civil money penalties, and corrective action plans linked to breaches.
Your region and entity type compared to national averages.
Full glossary — scoring methodology, source descriptions, threat classifications, vector definitions.
Data freshness, source status, last update timestamps per source.
Data integrity
01
Federal breach reporting for incidents affecting 500+ individuals. The mandatory disclosure standard for HIPAA-covered entities.
02
State-level breach notifications that frequently surface weeks before federal reporting. Currently tracking all 50 states.
03
Office for Civil Rights resolution agreements, civil money penalties, and corrective action plans tied to HIPAA violations.
04
Federal Trade Commission proceedings against entities handling health data outside HIPAA jurisdiction.
05
Critical infrastructure security advisories relevant to healthcare systems.
06
Threat observations from healthcare security professionals and practice managers across the Patient Protect network.
07
AI-derived risk indicators synthesized from cross-source pattern analysis, anomaly detection, and trend modeling.
Every source is visible simultaneously. The Geographic Map color-codes incident markers by data source — so you can see, at a glance, whether a regional threat cluster is driven by federal reporting, state AG action, or community intelligence.
Editorial coverage · From our partner publication
Editorial reporting on the breaches and enforcement actions in the dashboard above. Each story is paired with a Patient Protect operational response.
May 11, 2026 · Breach
Thousands of DICOM medical imaging servers belonging to hundreds of healthcare entities have been left exposed to the public internet with little or no authentication, putting patient data at direct risk.
Read on HIPAA Pulse
May 7, 2026 · Cybersecurity
CISA released new guidance urging critical infrastructure operators, including healthcare organizations, to invest in isolation and recovery capabilities to sustain operations during nation-state cyberattacks.
Read on HIPAA Pulse
May 7, 2026 · Cybersecurity
Dutch EHR vendor ChipSoft disclosed that stolen patient data was allegedly destroyed following a ransomware attack by the Embargo group, after the company confirmed some negotiations had taken place.
Read on HIPAA Pulse
May 6, 2026 · Breach
Missouri's Department of Commerce and Insurance is escalating its investigation into Conduent Business Services after the national insurance-processing vendor allegedly failed to cooperate with regulators over a breach potentially affecting millions of consumers.
Read on HIPAA Pulse
May 5, 2026 · Enforcement
The DOJ launched a new West Coast Health Care Fraud Strike Force, uniting federal prosecutors across Arizona, Nevada, and Northern California to pursue fraud schemes tied to digital health companies.
Read on HIPAA Pulse
May 4, 2026 · Breach
A CMS-built Medicare provider directory inadvertently exposed the Social Security numbers of healthcare providers in a backend database, The Washington Post reported.
Read on HIPAA Pulse
HIPAA Pulse is the editorial publication of Patient Protect. PP’s HIPAA Response translates each story into operational guidance.
What makes this different
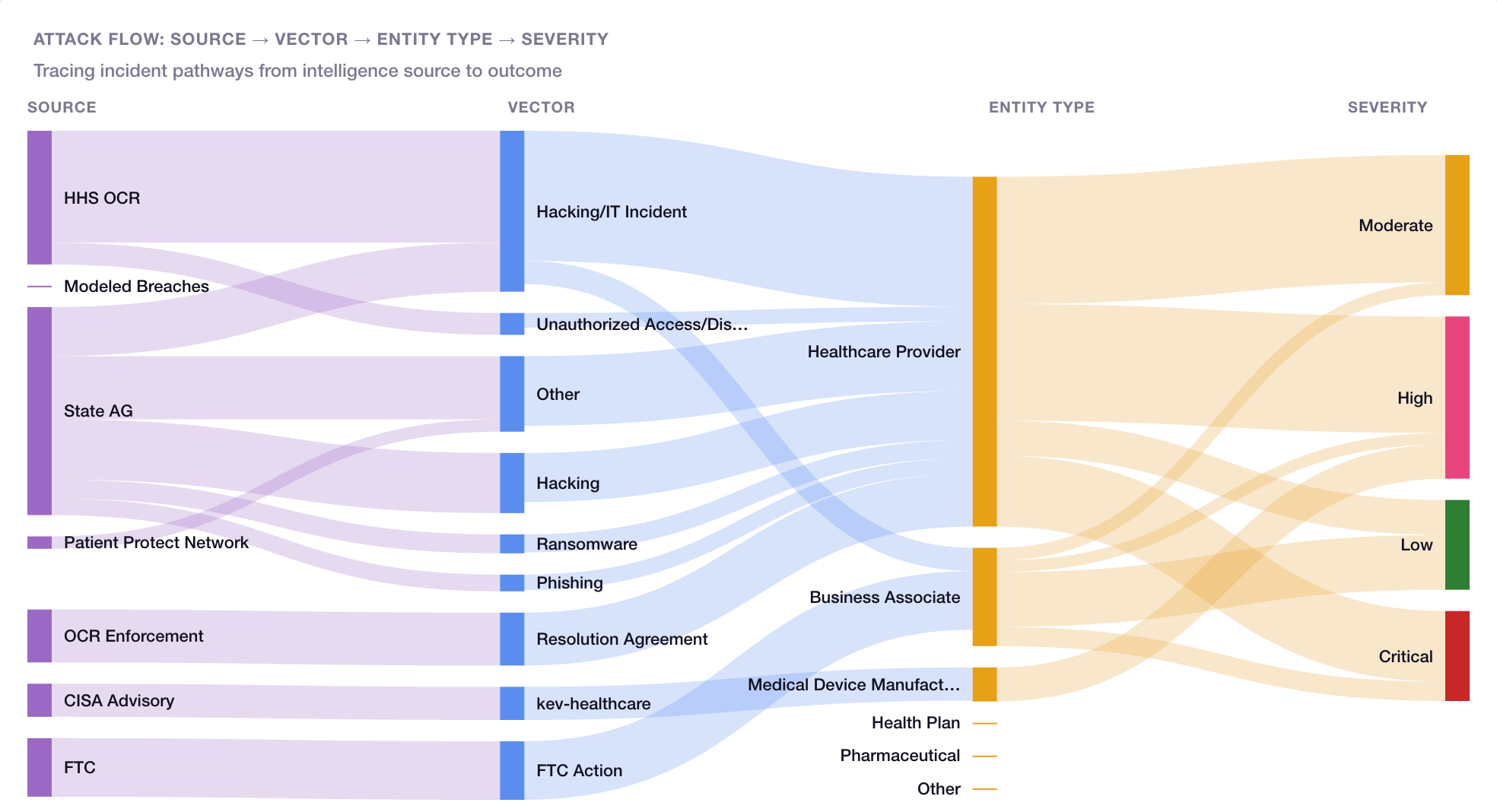
Attack chain visualization
The Attack Chains view traces every incident from its intelligence source through attack vector to entity type and severity outcome — revealing the most exploited pathways in real time.
Every unique attack vector mapped live
Top attack paths identified automatically
Dominant-vector clusters highlighted
The #1 attack vector is Hacking/IT Incident. See how Patient Protect addresses it.
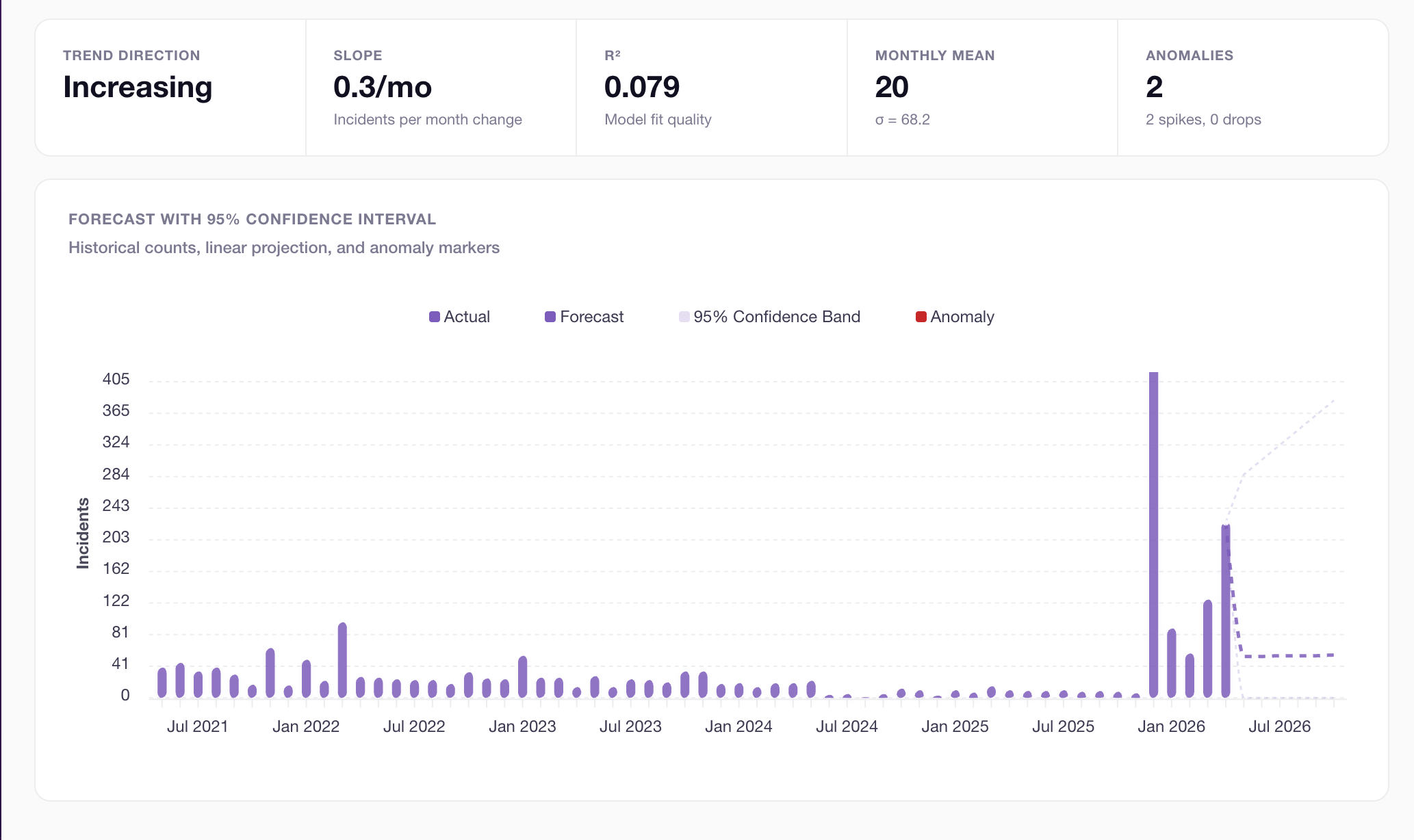
Predictive analytics
Risk Forecasting uses linear regression with R² confidence scoring and anomaly detection to project future incident volume. The threat surface is growing — the dashboard shows you exactly how fast.
Incident trend rate computed from 90-day average
Next-quarter projection with confidence band
Anomalous spikes flagged automatically
See how these projections relate to your practice. Take the free risk assessment.
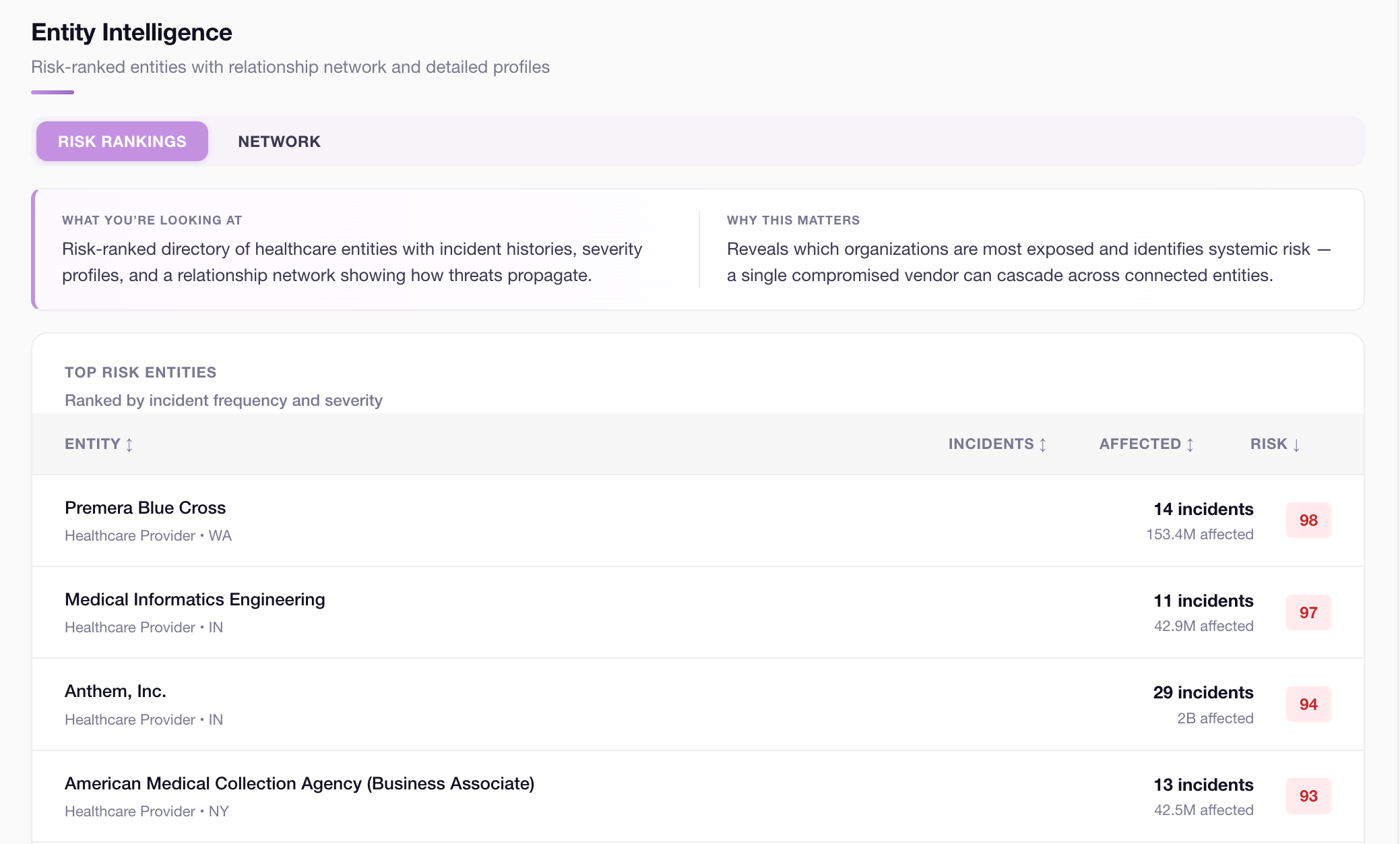
Entity risk rankings
Entity Intelligence ranks every healthcare organization by incident frequency, severity, and individuals affected. If you share data with any entity in this system, their risk score is part of your risk profile. A single compromised vendor can cascade across every connected entity.
Risk scores computed from live incident data
Repeat offenders flagged with trend velocity
Relationship network shows threat propagation
If a vendor breach exposes you, Patient Protect keeps your BAA documentation ready. See BAA management.
No gates · No signup · No cost
Enterprise threat intelligence platforms price these capabilities for organizations with dedicated security budgets. Patient Protect provides them at no cost because independent practices deserve the same threat visibility as hospital systems — regardless of budget.
No account required · Opens immediately
When you're ready for continuous compliance monitoring — see pricingFrom intelligence to action
The breach dashboard shows you the threat environment. Patient Protect gives you the controls to stay out of it — risk assessment, policy management, vendor tracking, and continuous compliance monitoring. Starting at $39/month.
14-day free trial · No charge until trial ends
Live dashboard
The Breach Intelligence Dashboard aggregates data from publicly available federal, regulatory, and community sources. By accessing this tool, you agree to the following:
Data Disclaimer
This data is provided “as-is” for informational and educational purposes only. It does not constitute legal, compliance, or professional advice. Certain records are algorithmically modeled from news sources and labeled accordingly. Patient Protect makes no warranties regarding accuracy, completeness, or timeliness. Inclusion of any entity does not imply wrongdoing. You are solely responsible for independently verifying information before relying on it.
Intellectual Property Agreement
The dashboard's aggregation methodology, scoring algorithms (Severity Score, Source Confidence, Overall Risk Score, Entity Risk Score), threat classification system, and analytical views are proprietary to Patient Protect LLC. Automated scraping, bulk export for commercial purposes, redistribution, and use in competitive products is prohibited. Use is subject to Patient Protect's Terms of Use and IP Policy.
Acceptance is stored locally for 30 days. No account required.
Subscribe to breach intelligence
HIPAA Pulse digests breach activity, OCR enforcement, and regulatory moves into one editorial briefing. Free, no spam, unsubscribe anytime — same intelligence powering this dashboard.
Every other Wednesday · Free · Unsubscribe anytime
FAQ
Yes. No login, no subscription, no trial period. Open it directly at patient-protect.com/breachdash. All twelve views are accessible immediately.
Seven sources: the HHS OCR Breach Portal, State Attorney General notifications from all 50 states, OCR Enforcement actions, FTC enforcement actions, CISA vulnerability advisories, Patient Protect network intelligence, and AI-modeled threat signals. Each source is identified in the dashboard by color code.
Updated nightly. HHS OCR and State AG data is ingested every night. The timestamp in the dashboard header shows the exact last update time for each source.
Yes. The Incident Explorer view supports CSV export of all records for compliance documentation, audit reporting, and custom analysis.
The HHS OCR portal shows you one source. This dashboard aggregates seven — including State AG notifications that often appear weeks before federal disclosure, FTC enforcement for non-HIPAA entities, CISA vulnerability advisories, and predictive models. It also adds analytical views — risk forecasting, attack chain visualization, entity risk rankings — that the federal portal doesn’t provide.
Independent practices are the fastest-growing target for healthcare cyberattacks — attacks on small providers have increased 6× since 2021. Understanding which breach types and attack methods are trending helps you prioritize the controls that actually prevent incidents at your practice.
Modeled breaches are AI-derived threat signals synthesized from patterns across all seven data sources. When the system detects anomalous clustering — unusual frequency, vector similarity, or geographic correlation — it generates modeled signals that flag emerging threats before they appear in official reporting.
The breach intelligence dashboard is free and open to everyone — no subscription required. Patient Protect subscribers get additional capabilities including practice-specific risk scoring, custom alerts, vendor monitoring, and integration with their compliance workflow.
The information provided through this dashboard is aggregated from publicly available sources, including but not limited to the U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR) Breach Portal, OCR Resolution Agreements, Federal Trade Commission (FTC) health breach notifications, state Attorney General breach notification databases, the Cybersecurity and Infrastructure Security Agency (CISA) advisories, and curated news reporting. Certain records are algorithmically modeled or AI-derived from news sources and are clearly labeled as such; these “modeled” entries represent projections based on public reporting and have not been confirmed by any regulatory authority.
This data is provided “as-is” for informational and educational purposes only and does not constitute legal, compliance, medical, financial, or professional advice. Patient Protect makes no representations or warranties, express or implied, regarding the accuracy, completeness, timeliness, reliability, or suitability of the data for any particular purpose. Source records may contain errors, omissions, delays, or inaccuracies originating from the underlying publishers, and may be updated, corrected, or withdrawn at any time without notice.
Inclusion of any organization, individual, incident, or enforcement action in this dataset does not imply wrongdoing, liability, guilt, non-compliance, or any adverse determination. References to specific entities reflect publicly reported information and should not be interpreted as an endorsement, accusation, or characterization by Patient Protect.
Users are solely responsible for independently verifying any information before relying on it for decision-making, regulatory reporting, business operations, journalism, research, or legal proceedings. Patient Protect, its affiliates, officers, employees, contributors, and data providers disclaim all liability for any direct, indirect, incidental, consequential, or punitive damages arising from the use of, reliance on, or inability to use this data.
Use of this dashboard is subject to applicable laws, the terms of service of original data sources, and Patient Protect's Terms of Use. Redistribution, resale, or commercial use may require separate authorization.
If this data hits close to home